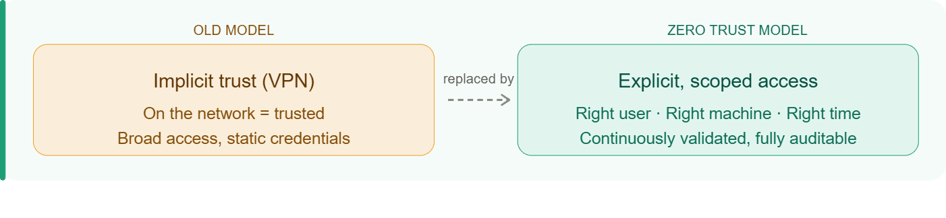
Zero Trust has become a familiar term in cybersecurity, but in industrial environments it is often misunderstood or oversimplified. For OEMs and manufacturers offering remote service, Zero Trust is not a theoretical security model. It is a practical framework for deciding who can access which machines, when, and under what conditions, without assuming anything is inherently safe.
Why traditional trust models break down in industrial environment
Historically, industrial systems relied on implicit trust:
- If you were on the network, you were trusted
- If a VPN was active, access was broadly permitted
- If credentials existed, they were often reused
This model made sense when systems were isolated and access was rare. It breaks down quickly once remote service, third-party access, and cloud connectivity are introduced.
Modern IIoT environments are always connected, accessed by multiple internal and external parties, and expected to operate continuously for years. Implicit trust does not scale in this reality.
What Zero Trust actually means for IIoT
Zero Trust in industrial remote service is not about blocking access. It is about controlling it precisely.
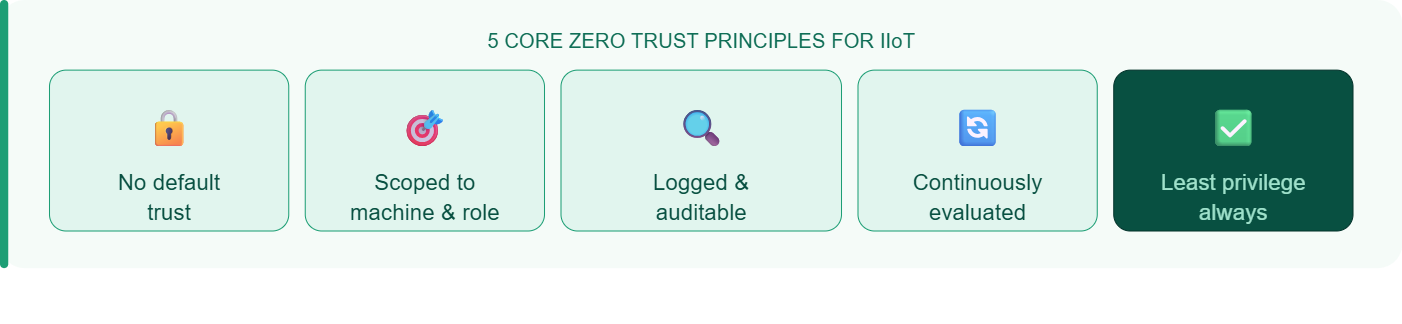
In practice, Zero Trust means:
- No user, device, or system is trusted by default
- Permissions are scoped to specific machines and functions
- Sessions are authenticated, logged, and auditable
- Trust is continuously evaluated
- Access is explicitly granted, not broadly assumed
This approach aligns closely with guidance from National Institute of Standards and Technology (NIST) and the International Society of Automation, both of which emphasize least privilege, segmentation, and lifecycle security as foundational OT principles.
ei³’s security architecture is designed around these principles, embedding Zero Trust concepts directly into industrial connectivity rather than layering them on afterward.
Why Zero Trust is different in industrial remote service
Zero Trust looks different in industrial environments than it does in IT.
Industrial systems must account for:
- Long equipment lifecycles
- Machines that cannot be easily patched or rebooted
- Safety and uptime constraints
- Customer-controlled networks
- Service teams that need fast, targeted access
A workable Zero Trust model for IIoT must be operationally realistic, not just theoretically secure.
The common mistake: VPNs masquerading as Zero Trust
Many organizations believe they have adopted Zero Trust because they use VPNs or secure tunnels.
In practice, VPNs often:
- Grant overly broad network access
- Rely on static or shared credentials
- Provide limited visibility into session activity
- Make it difficult to scope access by machine or role
The connection may be encrypted, but the trust model underneath it remains wide open.
Zero Trust focuses on who is accessing what, not just how they connect.
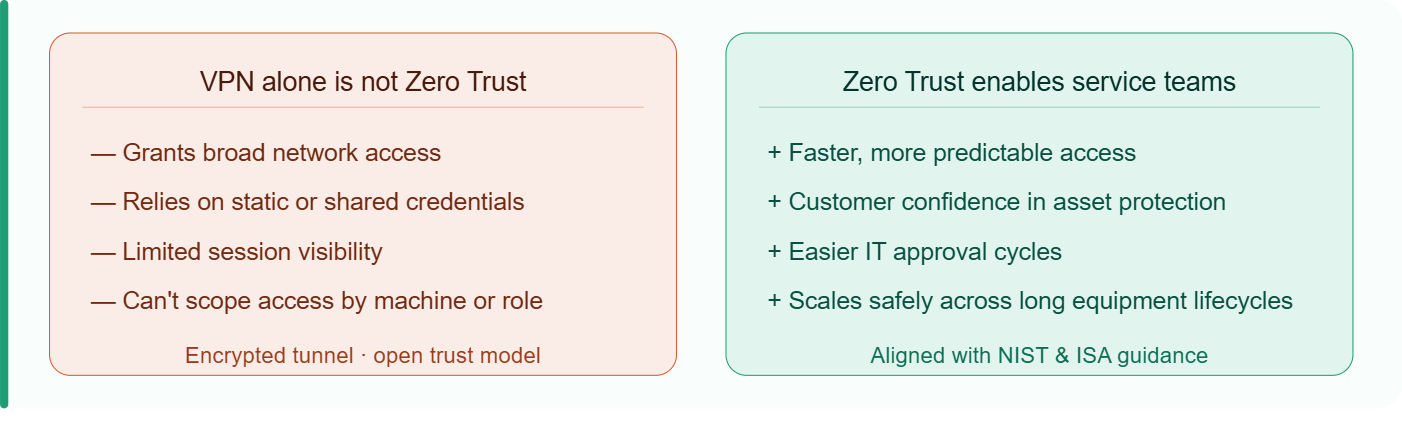
Why Zero Trust enables, rather than slows, remote service
A common concern is that Zero Trust will slow down service teams. In reality, it often removes friction.
When access is clearly scoped, centrally managed, and auditable by default:
- Service teams gain faster, more predictable access
- Customers gain confidence in how their assets are protected
- IT approval cycles become easier, not harder
Just as importantly, this kind of controlled, repeatable access is what allows remote service and IIoT initiatives to scale safely over time.
The ei³ SERVICE application applies Zero Trust principles directly to remote service workflows, enabling controlled, machine-level access without exposing broader customer networks.
Key Takeaway: When access is explicit, scoped, and continuously validated, remote service becomes safer, easier to scale, and easier to trust. Zero Trust is not about assuming nothing is safe. It is about ensuring only the right access exists.





